Is There Value in Being a Certified Ethical Hacker? Research Says Yes
A new report provides a comprehensive look at the value of Certified Ethical Hacker (CEH) credentials.
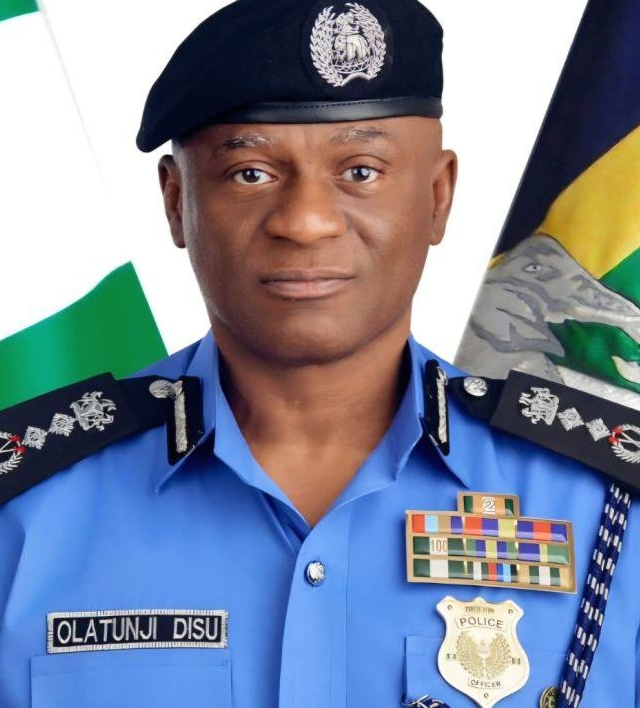
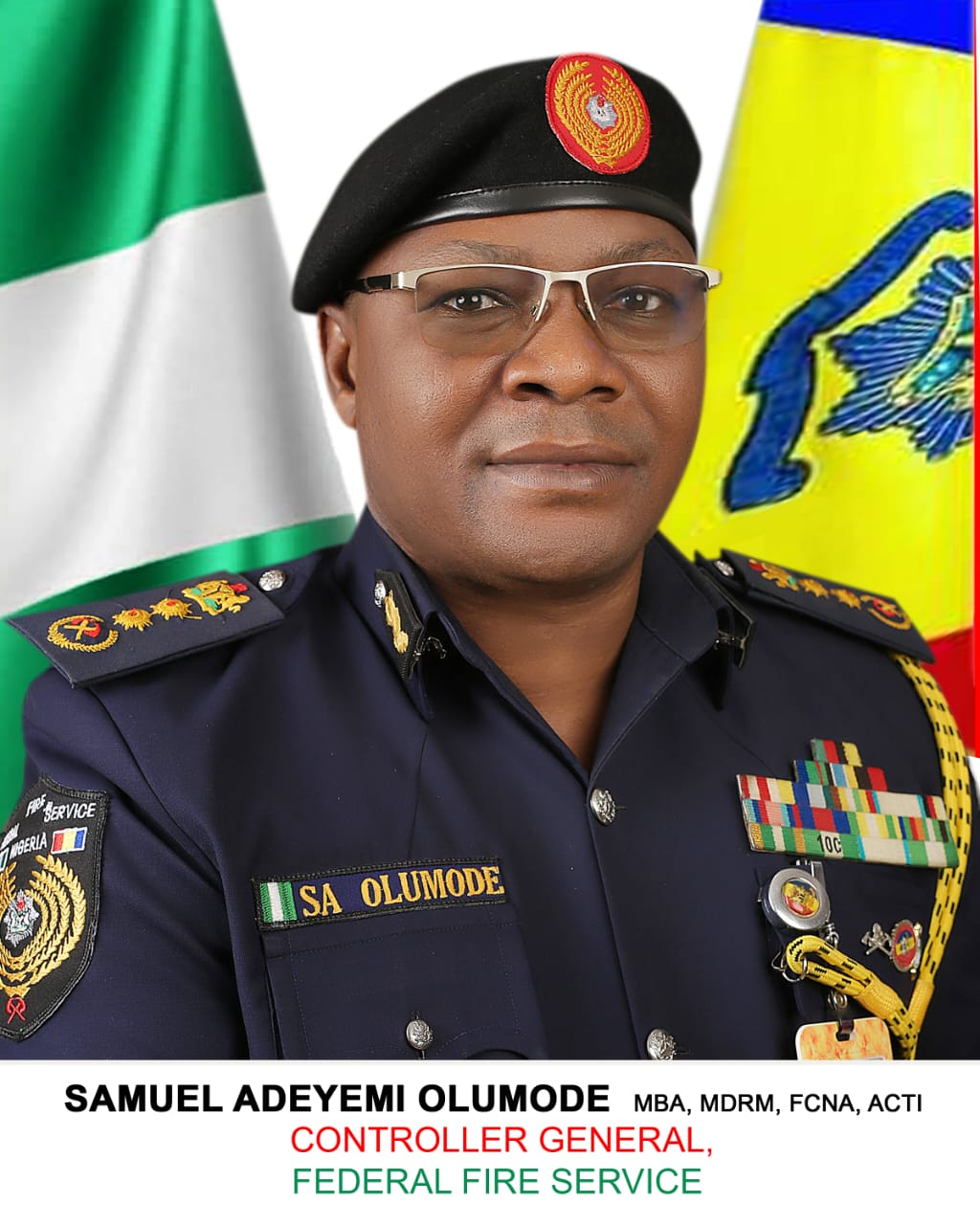
FG Launches Crackdown on Job Scam Syndicates Targeting NSCDC, Immigration, Fire Service, NCoS Applicants
The Federal Government has initiated a coordinated crackdown on fraud syndicates attempting to deceive job seekers applying for recruitment into paramilitary agencies under the Ministry of Interior. This was disclosed…
Scattered Spider’s Newest Targets: Transportation and Airlines
Scattered Spider is evolving tactics and targeting new sectors.
DevOps Missteps Fuel Crypto-Mining: Why Infrastructure Observability Is a Security Imperative
Cryptojacking is often treated as a nuisance-level threat, but recent campaigns have exposed a far more systemic issue.
COMMANDANT AHMAD ATTENDS NBA KATSINA 2025 LAW WEEK
The State Commandant, Nigeria Security and Civil Defence Corps (NSCDC) Katsina State Command, Commandant of Corps Aminu Datti Ahmad fsf, MADM, FCAI, graced the 2025 law week organized by the…
1 in 20 Financial Service Online Identity Verification Attempts Is Fraudulent
1 in 20 online identity verification attempts are fraudulent in the financial services sector.
Armed Forces Radio Has Countered Terrorist Propaganda and Misinformation, Says CDS
Pix: General Christopher Musa, Chief of Defence Staff By Hammed Ibrahim, Abuja The Chief of Defence Staff, General Christopher Gwabin Musa, has stated that the establishment of Armed Forces Radio…
Making Data Protection an Organizational Priority
In an era when data needs to be recognized as an asset in order to transform as a business, retrieving value from data becomes the topmost priority.
Tinubu Extends Customs CG Adeniyi’s Tenure by One Year to Complete Key Reforms
By Chuks Nnamdi, Abuja President Bola Ahmed Tinubu has approved a one-year extension for the Comptroller-General of the Nigeria Customs Service (NCS), Bashir Adewale Adeniyi, whose initial tenure was scheduled…
AI Introduces Security Vulnerabilities Within Code in 45% of Cases
A recent report by Veracode revealed that while AI produces functional code, it introduces security vulnerabilities in 45% of cases.
 How CSOs Can Win Board Support for Gunshot Detection Technology
How CSOs Can Win Board Support for Gunshot Detection Technology What Are Security Experts Saying About OpenAI’s GPT-5.4-Cyber?
What Are Security Experts Saying About OpenAI’s GPT-5.4-Cyber? What “The Pitt” Gets Right About Ransomware and What Hospitals Can’t Afford to Ignore
What “The Pitt” Gets Right About Ransomware and What Hospitals Can’t Afford to Ignore NSCDC Inaugurates Madagwa Hausawa Divisional Office to Strengthen Grassroots Security in Nasarawa State
NSCDC Inaugurates Madagwa Hausawa Divisional Office to Strengthen Grassroots Security in Nasarawa State Democratized Software, Democratized Risk: Who’s Accountable When Everyone Codes?
Democratized Software, Democratized Risk: Who’s Accountable When Everyone Codes? PEOPLE’S SECURITY MONITOR: Military Launches Intelligence Training to Counter Terrorist Ambushes
PEOPLE’S SECURITY MONITOR: Military Launches Intelligence Training to Counter Terrorist Ambushes Borno Burial: Army Honours Fallen Brigadier General, Soldiers Killed by Terrorists
Borno Burial: Army Honours Fallen Brigadier General, Soldiers Killed by Terrorists 15th April, 2026Kwara NSCDC Commandant Pledges Tough Crackdown on Crime, Calls for Stronger Collaboration
15th April, 2026Kwara NSCDC Commandant Pledges Tough Crackdown on Crime, Calls for Stronger Collaboration McGraw Hill Data Breach Caused by Salesforce Misconfiguration
McGraw Hill Data Breach Caused by Salesforce Misconfiguration