Why SASE Should Be As Flexible as the Organization
SASE itself isn’t a catch-all, however. There are different types of SASE, and the differences between them can make or break whether or not they’re the right fit for your…
Think You Can’t Afford Recovery and Remediation? Think Again. You Have Everything to Lose
Businesses that can’t recover rapidly and control their losses could be lost forever.
47% of Manufacturing Breaches in 2024 Involved Ransomware
KnowBe4 released its new report highlighting cybersecurity challenges facing the manufacturing industry.
New ZuRu Malware Variant Targeting Developers
A new report reveals new artifacts associated with ZuRu, an Apple macOS malware.
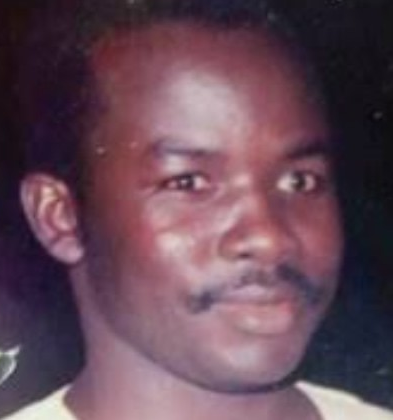
Tribute: General Buhari’s Military Brilliance: The Cameroon Episode
Abdulmumuni Kazaure, a military analyst, writes from London. In the annals of Nigeria’s military history, few figures cast a shadow as long or as controversial as General Muhammadu Buhari. Before…
Illegal Bunkering: Nigerian Army Arrests 50 Suspects in Niger Delta
Troops of the 6 Division of the Nigerian Army have arrested 50 individuals suspected of engaging in illegal bunkering and the refining of petroleum products across various parts of the…
Reframing ROI in Cybersecurity: From Cost Center to Business Enabler
As cyber budgets expand and boards demand clearer justification for security spend, CISOs and cybersecurity leaders must rethink how they define and demonstrate return on investment (ROI).
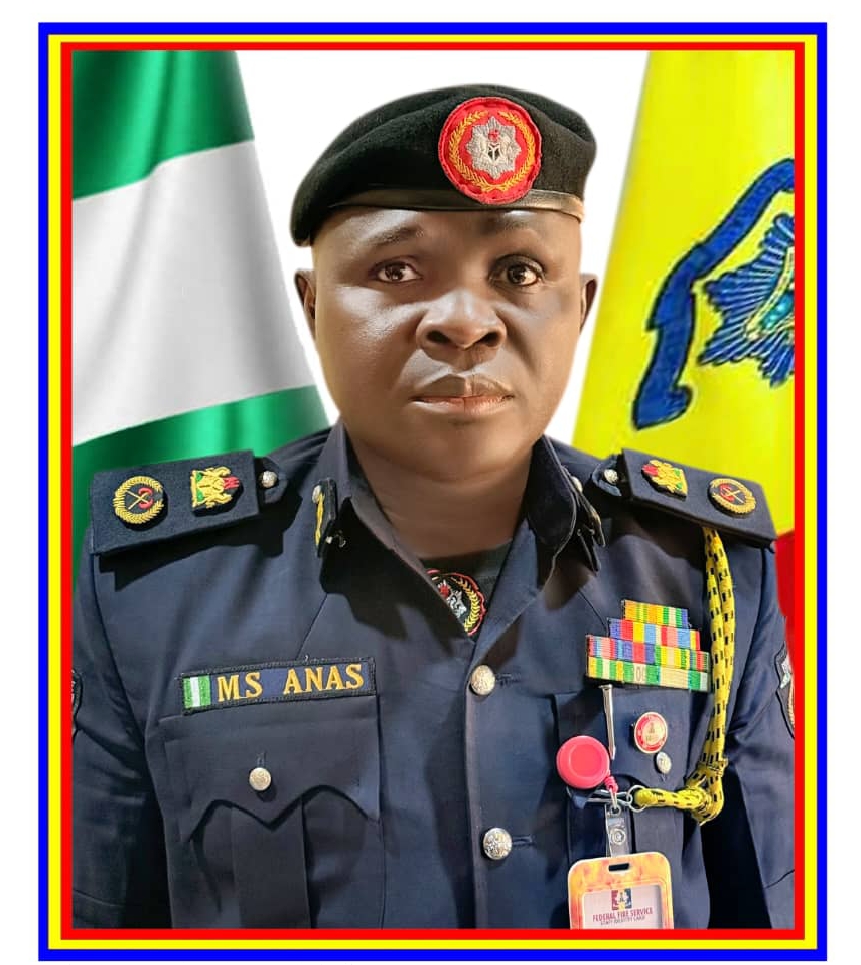
KATSINA NSCDC DEPLOYS 2807 OPERATIVES AHEAD OF THE BURIAL OF FORMER PRESIDENT MUHAMMADU BUHARI
The State Commandant, Nigeria Security and Civil Defence Corps,(NSCDC) Katsina State Command, Commandant of Corps Aminu Datti Ahmad deployed 2807 operatives ahead of the burial of His Excellency Former President…
Nearly 250,000 Records From Tax Credit Consulting Agency Exposed
Research has uncovered an unencrypted, non-password-protected database containing 245,949 records.
4 Critical, Known Exploited Vulnerabilities Added to KEV Catalog
CISA added 4 new vulnerabilities to the Known Exploited Vulnerabilities (KEV) Catalogue, citing evidence of active exploitation.
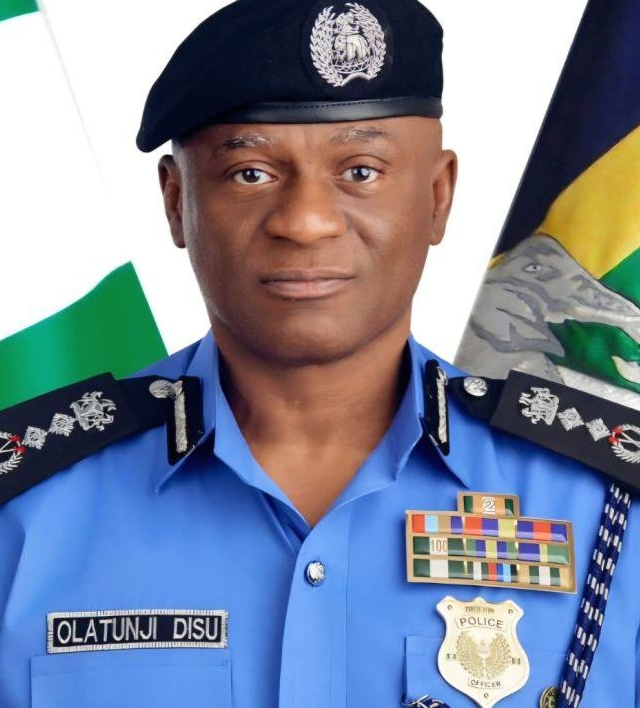 Ondo Police Leadership Shake Up Follows Allegations of Unauthorised Financial Deductions
Ondo Police Leadership Shake Up Follows Allegations of Unauthorised Financial Deductions Foxconn Confirms Cyberattack, Security Experts Discuss
Foxconn Confirms Cyberattack, Security Experts Discuss Expert Insights on the West Pharmaceutical Ransomware Attack
Expert Insights on the West Pharmaceutical Ransomware Attack The Bench You’ll Need in Three Years Depends on Decisions You Make Now
The Bench You’ll Need in Three Years Depends on Decisions You Make Now What Security Leaders Say About the First AI-Developed Zero-Day Exploit
What Security Leaders Say About the First AI-Developed Zero-Day Exploit Cybersecurity Is No Longer a Gatekeeper, But the Engine of Delivery Across Digital Economy
Cybersecurity Is No Longer a Gatekeeper, But the Engine of Delivery Across Digital Economy Customs Intercepts Undeclared $461,600 at Kano Airport, Transfers Suspects to EFCC
Customs Intercepts Undeclared $461,600 at Kano Airport, Transfers Suspects to EFCC MINING MARSHALS, MINISTRY INTENSIFY JOINT OPERATIONS AGAINST ILLEGAL MINING
MINING MARSHALS, MINISTRY INTENSIFY JOINT OPERATIONS AGAINST ILLEGAL MINING Why Security Leaders Need to Move Beyond the Mental Illness Narrative
Why Security Leaders Need to Move Beyond the Mental Illness Narrative SERAP Appeals ₦100m Defamation Judgment Against DSS Officials, Seeks Stay of Execution
SERAP Appeals ₦100m Defamation Judgment Against DSS Officials, Seeks Stay of Execution