Sudo Vulnerability Discovered, May Exposes Linux Systems
Sudo, the privileged command-line tool often installed on Linux systems, has two local privilege vulnerabilities.
Increase in Identity-Based Attacks Attributed to Infostealers
Info-stealing malware and advanced phishing kits account for 156% increase in cyberattacks that target user logins.
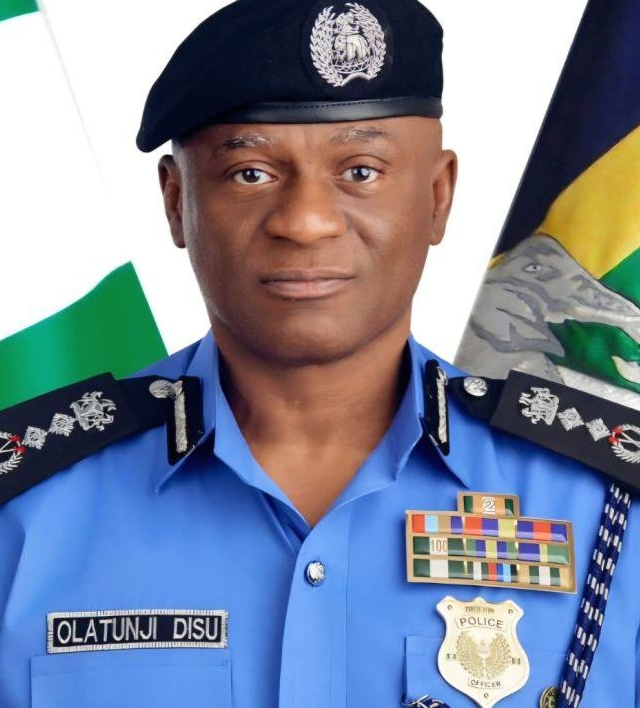
Nigerian Army Foils Bandit Attacks in Kebbi, Neutralises Dozens
Troops of the 223 Light Battalion of the Nigerian Army, based in Zuru, have successfully repelled a large-scale attack by armed bandits on Ribah town in Danko-Wasagu Local Government Area…
Gunmen Ambush Security Team in Benue, Kill 2 NSCDC Officers, Injure Others
Armed men suspected to be herders have reportedly ambushed a joint security patrol in Benue State, killing two personnel of the Nigeria Security and Civil Defence Corps (NSCDC), injuring three…
Security Through Quality: Navigating the Latest Cybersecurity Executive Order
The recent Executive Order from the Trump Administration, while modifying some prior requirements, underscores a crucial truth: agencies still bear the unchanged responsibility of safeguarding mission and data.
Security Leaders Discuss Marco Rubio AI Imposter
Secretary of State Marco Rubio was recently impersonated via text messages and AI voice messages.
How to Prevent “Smash & Grab” Cyberattacks
The best way to prevent smash & grab cyberattacks is to safeguard shared drives and implement MFA protection in a timely manner.
Threat Actor Targeting Indian Defense Sector
A threat actor based in Pakistan (APT36) has engaged in a sophisticated cyber-espionage campaign.
OT Security Responsibility Is Elevating to Executive Leadership
New research delves into the state of operational technology (OT) cybersecurity.
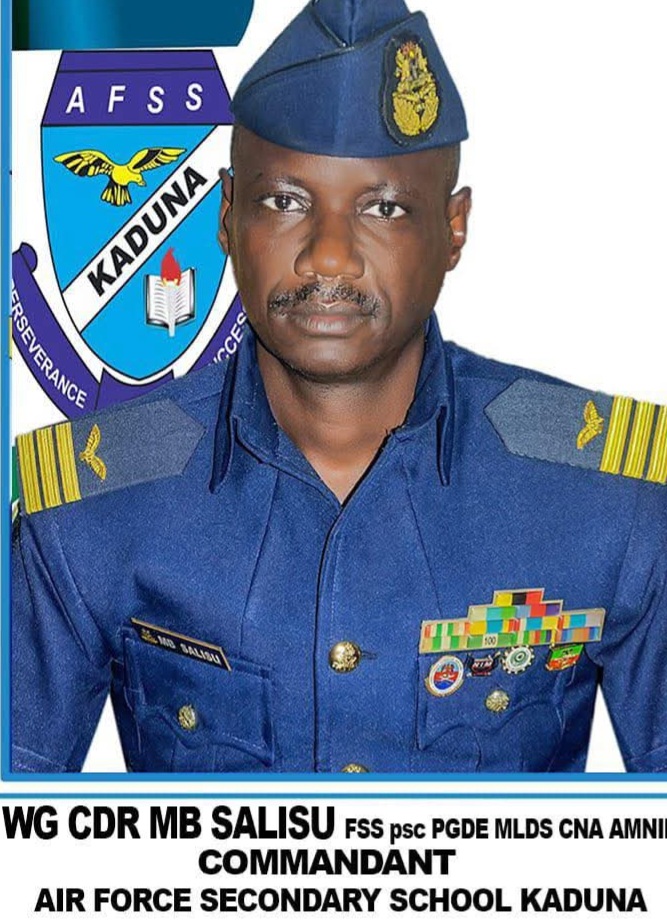
 Navy Captain Umar Bakori (Rtd), National Chairman/Commander General, to Speak on how “Falling Military Recruitment Threatens Nigeria’s Internal Security”
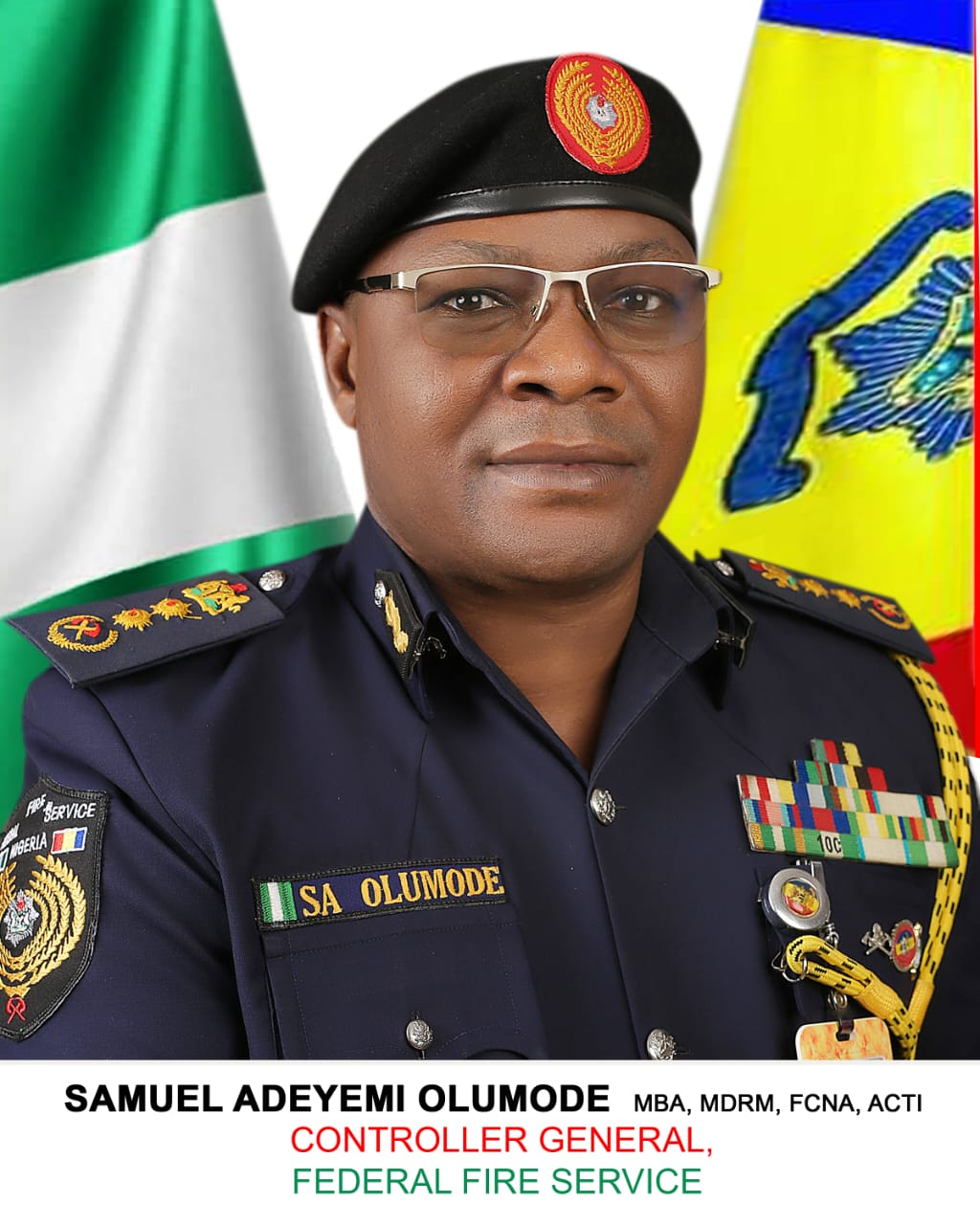
Navy Captain Umar Bakori (Rtd), National Chairman/Commander General, to Speak on how “Falling Military Recruitment Threatens Nigeria’s Internal Security” FFS Gombe Issues Safety Advisory on Rooftop Solar Installations
FFS Gombe Issues Safety Advisory on Rooftop Solar Installations US Security Agency Leverages Claude Mythos Despite Pentagon Blacklist
US Security Agency Leverages Claude Mythos Despite Pentagon Blacklist Vercel Breach Originated From an Employee’s AI Tool
Vercel Breach Originated From an Employee’s AI Tool 58% of Organizations Spend Over 10 Hours a Month Securing AI-generated Code
58% of Organizations Spend Over 10 Hours a Month Securing AI-generated Code Advance Your Cybersecurity Career
Advance Your Cybersecurity Career Nigerian Navy dismantles 22 illegal refineries, recovers 457,000 litres of stolen oil in three months
Nigerian Navy dismantles 22 illegal refineries, recovers 457,000 litres of stolen oil in three months Top 3 Cyber Insurance Incident Claims
Top 3 Cyber Insurance Incident Claims