Security Leaders Discuss the Claude Mythos Breach
What security experts are saying about the Claude Mythos breach.
Operationally Ineffective: Putting CVEs in a Chokehold with Privilege Disruption
While vulnerability management and patching remain necessary, they are not sufficient to address the new reality that Mythos represents.
NIST’s New Prioritization Criteria for CVEs, Examined by Experts
NIST recently changed how it handles CVEs.
How Should Effective AI Red Teams Operate?
Dr. Peter Garraghan speaks with Security magazine about AI-specific red teaming.
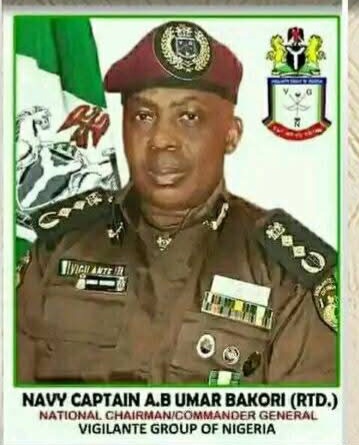
Kwara Governor Receives New NSCDC Commandant, Pledges Sustained Support for Security
The Executive Governor of Kwara State, AbdulRahman AbdulRazaq, on Tuesday, 21 April 2026, received the newly deployed State Commandant of the Nigeria Security and Civil Defence Corps, Kwara State Command,…
Unauthorized Users Accessed Claude Mythos, New Reports Suggest
Anthropic’s new AI model may have been accessed by unauthorized users.
Why Bridging Siloes Doesn’t Need to Be Complicated
Bruce McIndoe discusses provides actionable steps for bridging siloes.
Hackers Claim 19M Records Stolen From French Government Agency
The France Titres discovered a security incident.
The Security Metric That’s Failing You
Security teams have measured patch rates for so long that somewhere along the way, the metric became the strategy.
The Privacy–Security Partnership: How We Bend Risk in a Resource Crunch
The partnership between cybersecurity and privacy matters now more than ever.
 Nigerian Navy Launches Exercise Obangame Express 2026 to Strengthen Gulf of Guinea Security
Nigerian Navy Launches Exercise Obangame Express 2026 to Strengthen Gulf of Guinea Security Nigerian Army Destroys Suspected IPOB/ESN Camp in Imo, Recovers Remains of Slain Personnel
Nigerian Army Destroys Suspected IPOB/ESN Camp in Imo, Recovers Remains of Slain Personnel NYSC Reaffirms Commitment to Corps Members’ Safety and Welfare
NYSC Reaffirms Commitment to Corps Members’ Safety and Welfare Police Foil Attempted Bomb Attack at Ikot Ekpene Correctional Centre
Police Foil Attempted Bomb Attack at Ikot Ekpene Correctional Centre 2025 Saw Fewer Healthcare Breaches Than 2024
2025 Saw Fewer Healthcare Breaches Than 2024 Less Than 10% of Higher Education Has No Intention of Adopting AI
Less Than 10% of Higher Education Has No Intention of Adopting AI FIRST LADY COMMISSIONS INFRASTRUCTURAL PROJECTS IN MAIDUGURI
FIRST LADY COMMISSIONS INFRASTRUCTURAL PROJECTS IN MAIDUGURI What the Medtronic Breach Means for Security Experts
What the Medtronic Breach Means for Security Experts Why Energy Infrastructure Is Cybersecurity’s Next Frontier
Why Energy Infrastructure Is Cybersecurity’s Next Frontier