Product Spotlight on Access Control
Security magazine highlights a few access control products for 2026.
3 Hospital Security Guards Assaulted
A man was arrested after assaulting three security officers.
93% of Organizations Use or Plan to Use AI Agents for Sensitive Security Tasks
Organizations are handing AI the keys to sensitive systems before securing guardrails around those identities.
2.6M Accounts Exposed in DentaQuest Data Breach
Threat actors released the sensitive data of 2.6 million accounts.
How Hotels Can Stay on Top of Security During Travel Season
The security teams for hotels and other lodging accommodations often have less bandwidth during heightened traveling periods. Effective visitor management systems can support them.
The Hidden Security Risks Behind Popular AI Tools
To understand the real AI security challenge, it is important to look at how widely used AI tools are entering everyday workflows and where each can create exposure.
7 Data Security Stories to Know About (May 2026)
Security magazine takes a look at 7 data security stories from this month.
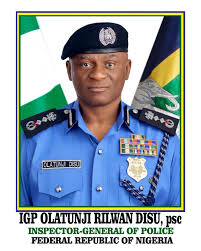
How the Current Iran-US Conflict May Impact World Cup Security
Political tensions involving Iran are multi-pronged and create a uniquely sensitive environment surrounding fan activity and demonstrations.
Security Experts Discuss Threats to FIFA World Cup 2026
This year’s World Cup presents an attractive opportunity for cybercriminals.
Schrödinger’s Vulnerabilities: What Mythos Actually Broke in Cyber Insurance
AI collapsed the discovery half of the vulnerability lifecycle from a slow, distributed, semi-public process into a fast, concentrated, partially-private one.