2026 People’s Security Monitor Security Summit: IGP Hails Tinubu’s Security Reforms, Says Collective Action Key to Defeating Insecurity
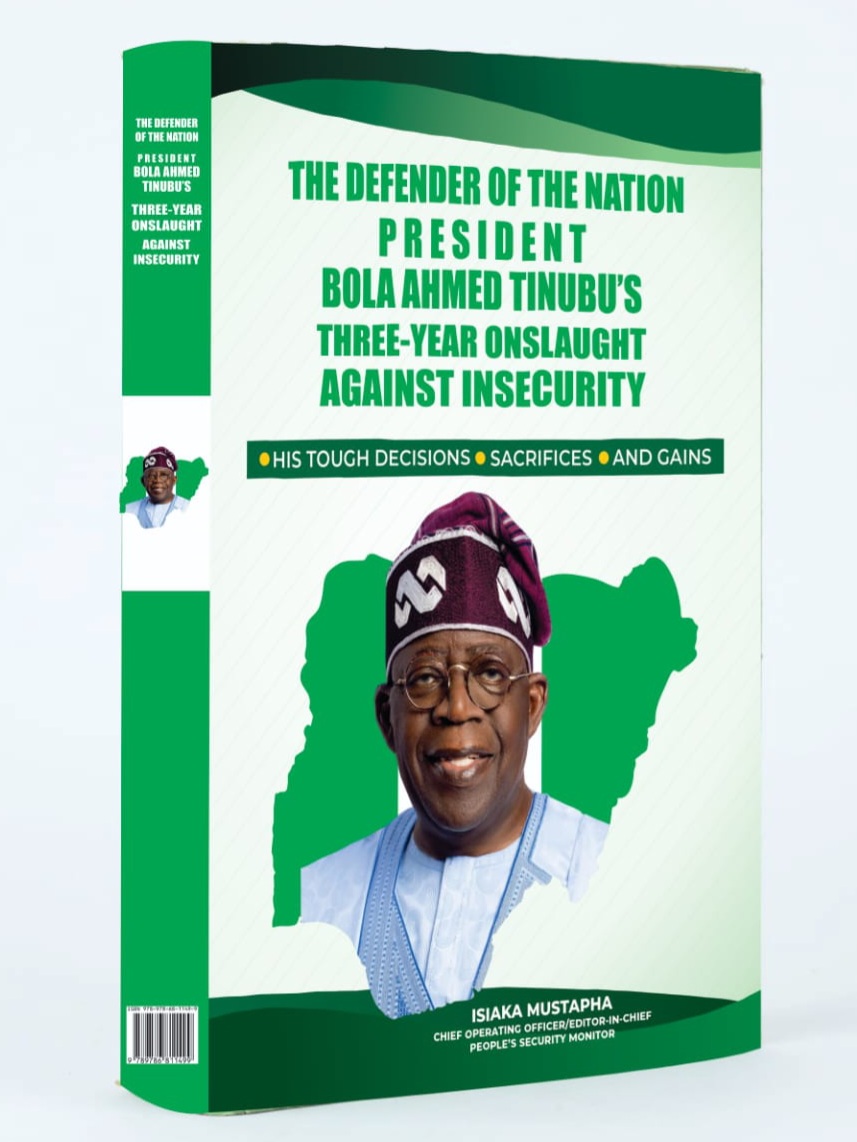
Address by the Representative of the Inspector General of Police, ACP Umar Yakubu, psc(+), FSPSP, FSI At the Public Presentation of the Book: The Defender of the Nation: President Bola Ahmed…
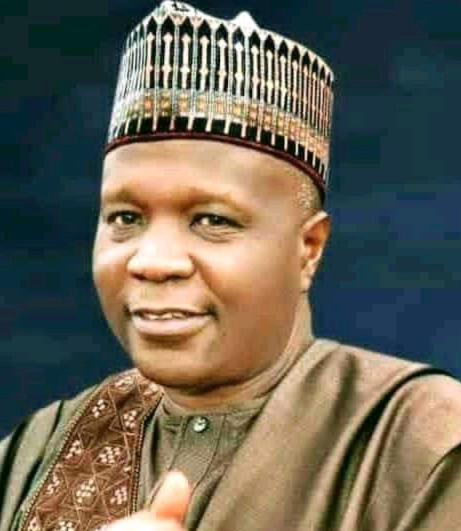
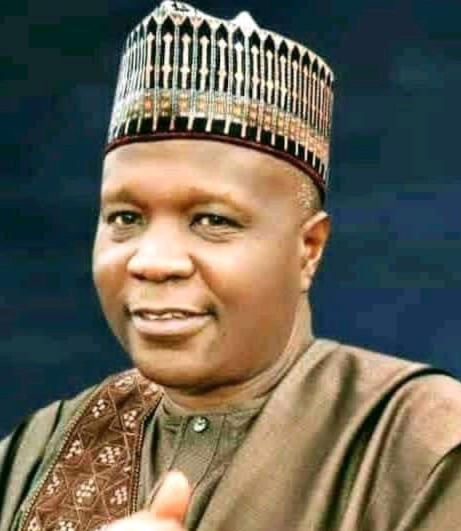
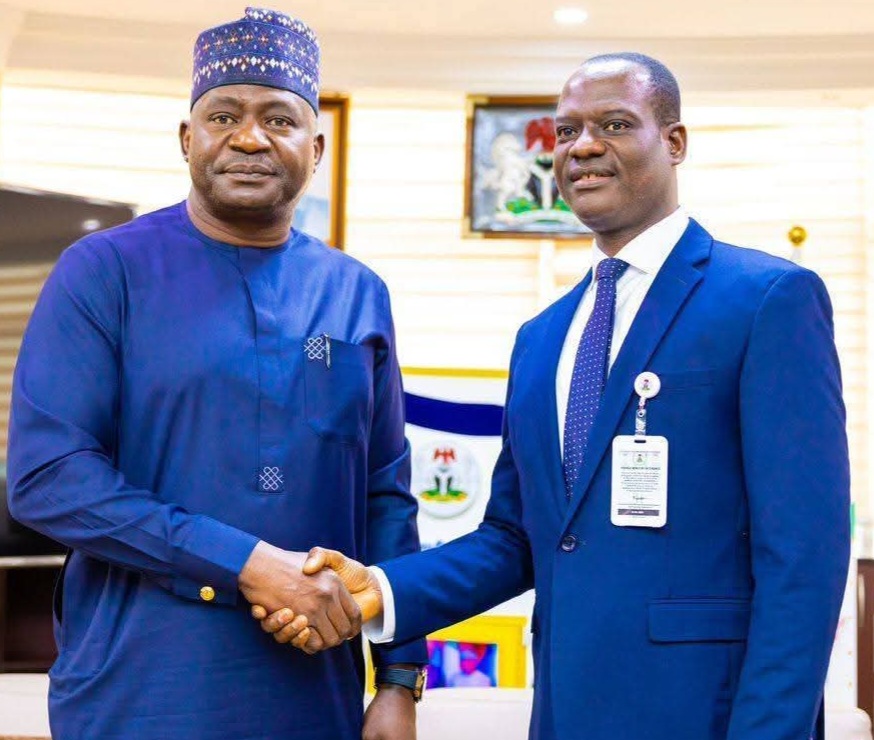
Gombe Emerges Nigeria’s Most Secure State as Governor Inuwa Yahaya Receives National Security Leadership Award
Pix: Gov. Yahaya Governor Muhammadu Inuwa Yahaya of Gombe State has been honoured with the prestigious 2026 Nigeria’s Most Secure State Excellence Award in recognition of his administration’s remarkable achievements…
2026 People’s Security Monitor Security Summit: Our Appreciation
The Management and Editorial Board of the People’s Security Monitor wishes to extend its profound and heartfelt appreciation to all distinguished guests, stakeholders, security leaders, partners, and participants who honoured…
2026 PSM SECURITY SUMMIT: OUR APPRECIATION
The Management and Editorial Board of the People’s Security Monitor will like to extend its profound and heartfelt appreciation to all distinguished guests, stakeholders, security leaders, partners, and participants who…
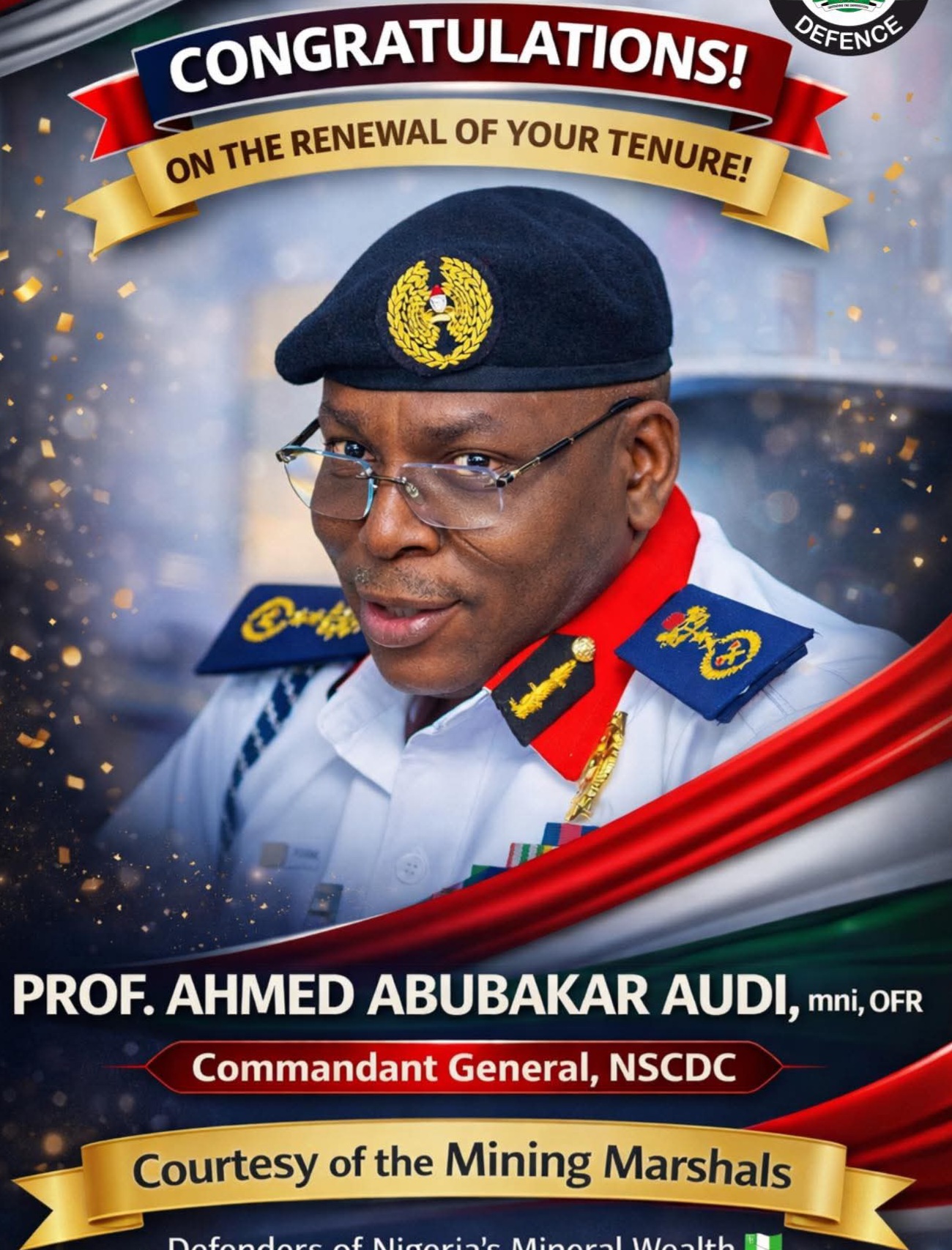
People’s Security Monitor Confers 2026 Exceptional Leadership Award on Ondo NSCDC Commandant Ibiloye…Dedicates Award to Ondo NSCDC Personnel
The Commandant of the Nigeria Security and Civil Defence Corps (NSCDC), Ondo State Command, Commandant Ibiloye, has expressed appreciation after being conferred with the 2026 Exceptional Leadership in Civil Defence…
BREAKING: EMIR OF ARGUNGU CALLS FOR LEGAL COMMUNITY SELF-PROTECTION MEASURES AGAINST BANDITRY
The Emir of Argungu, Alhaji Muhammad Samaila Mera, has called on residents of his emirate to take lawful steps to strengthen their personal and community security in response to the…
ONDO NSCDC Commandant Earns National Recognition for Exceptional Leadership in Civil Defence Operations
The Commandant of the Nigeria Security and Civil Defence Corps (NSCDC), Ondo State Command, Oluyemi Joshua Ibiloye, has been honoured with the prestigious 2026 Exceptional Leadership in Civil Defence Operations…
FEDERAL FIRE SERVICE KWARA COMMAND HOSTS AL-WAHYAIN INTERNATIONAL ACADEMY STUDENTS ON FIRE SAFETY EDUCATIONAL EXCURSION
The Federal Fire Service (FFS), Kwara State Command, under the leadership of the State Controller, ACF Bakare Mary, hosted students of Al-Wahyain International Academy (AIA), Ilorin, during an educational excursion…


 NAF Deploys Surveillance Aircraft to Aid Rescue of Abducted Oyo Teachers, Pupils
NAF Deploys Surveillance Aircraft to Aid Rescue of Abducted Oyo Teachers, Pupils Police Arrest Four Suspects, Kill Two in Rescue Operation for Adelabu’s Sister in Ibadan
Police Arrest Four Suspects, Kill Two in Rescue Operation for Adelabu’s Sister in Ibadan 2026 People’s Security Monitor Security Summit: Support Genuine Efforts to Secure Nigeria, Stop Politicising Insecurity – People’s Security Monitor Editor-in-Chief
2026 People’s Security Monitor Security Summit: Support Genuine Efforts to Secure Nigeria, Stop Politicising Insecurity – People’s Security Monitor Editor-in-Chief 2026 People’s Security Monitor Security Summit: Support Genuine Efforts to Secure Nigeria, Stop Politicising Insecurity – People’s Security Monitor Editor-in-Chief
2026 People’s Security Monitor Security Summit: Support Genuine Efforts to Secure Nigeria, Stop Politicising Insecurity – People’s Security Monitor Editor-in-Chief 2026 People’s Security Monitor Security Summit: Human Security Central to Nigeria’s Stability, Says Fire Service Controller General, Samuel Olumode Adeyemi
2026 People’s Security Monitor Security Summit: Human Security Central to Nigeria’s Stability, Says Fire Service Controller General, Samuel Olumode Adeyemi Operation Hadin Kai Rescues 360 Kidnap Victims in Major Offensive Against Terrorists in Borno
Operation Hadin Kai Rescues 360 Kidnap Victims in Major Offensive Against Terrorists in Borno 2026 People’s Security Monitor Security Summit: How Gombe Became a Beacon of Peace Amid Regional Security Challenges – Governor Yahaya
2026 People’s Security Monitor Security Summit: How Gombe Became a Beacon of Peace Amid Regional Security Challenges – Governor Yahaya 2026 People’s Security Monitor Security Summit: IGP Hails Tinubu’s Security Reforms, Says Collective Action Key to Defeating Insecurity
2026 People’s Security Monitor Security Summit: IGP Hails Tinubu’s Security Reforms, Says Collective Action Key to Defeating Insecurity